Personal Data Vault
Encryption doesn't have to be a black box. Let's explore how we use a "Double-Lock" strategy to keep your financial life private.
The "Mailbox & House Key" Analogy
Imagine your data is inside your house. How do we make sure only you can enter?
1. The Mailbox Key
Your Master Password is like a key to a small mailbox outside your house. This mailbox doesn't contain your money—it only contains the real key to your home.
2. The House Key
Inside the mailbox is your Data Encryption Key (DEK). This is a special, high-security key that actually unlocks your financial records. It never leaves your device in a way that anyone else can use.
The "600,000 Boxes" Challenge
To make it even harder for intruders, we don't just put the House Key in the mailbox. We place it inside 600,000 nested lockboxes. Every time you log in, your device uses your password to open each box one by one. This process takes about a second for you, but it's a nightmare for hackers.
Why Iterations Matter?
Hackers use "Brute Force"—trying millions of passwords every second using supercomputers.
Without 600k Iterations
Guesses per second on a high-end GPU
With SMT's 600k Iterations
Guesses per second (forced slowness)
* Estimates based on modern high-performance GPU benchmarks (e.g., RTX 4090).
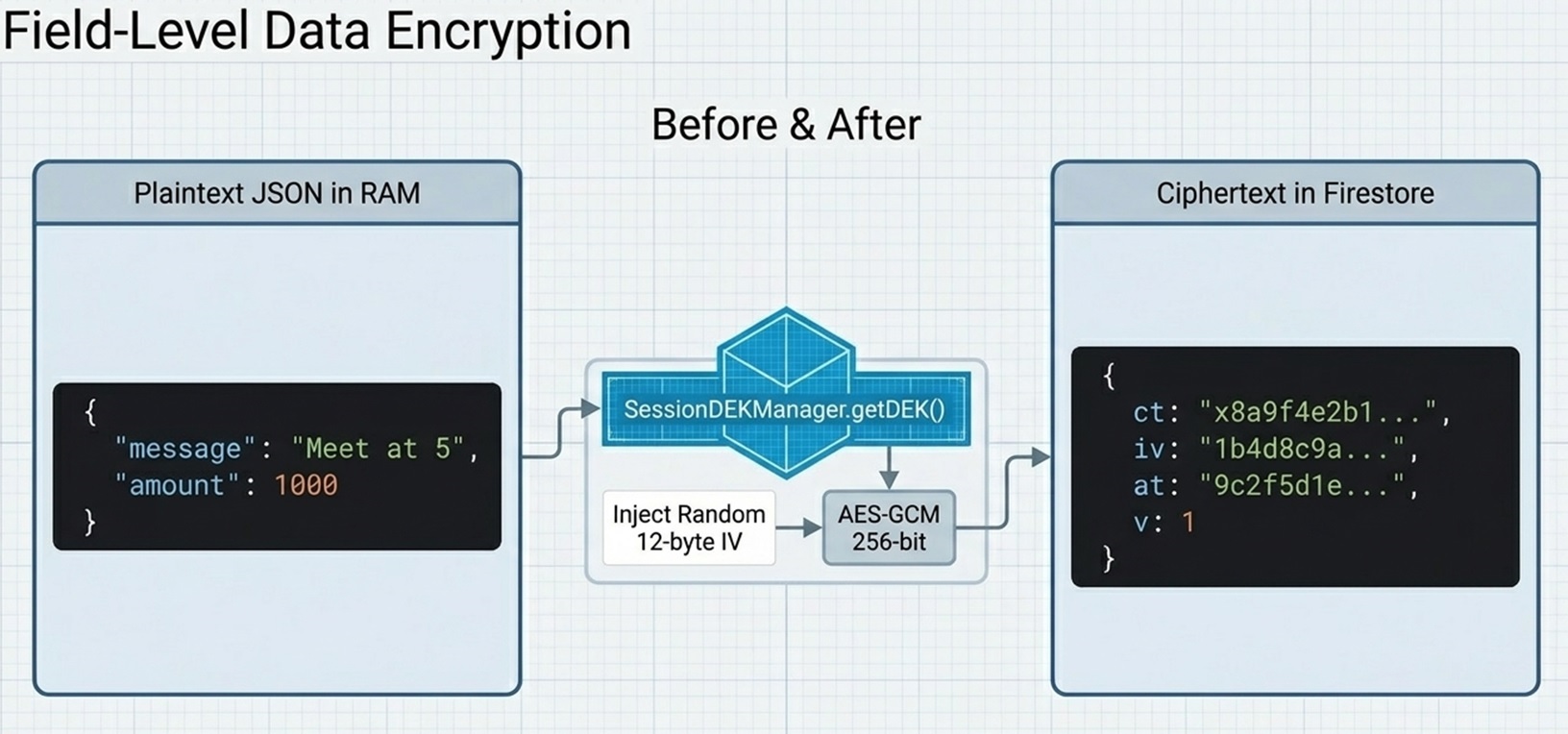
The Technical Blueprint
How your data flows from your brain to the secure database.
Personal Data
Firestore
What Data is Protected?
Our KEK/DEK architecture covers almost every piece of sensitive information you store in SimpleMoneyTracker.
Expenses
Description, Amount, Category, Mood, Date
Budgets
Budget Amounts, Timeframes
Debts & Lending
Lender/Borrower names, Amounts, Due dates, Notes
Financial Goals
Goal names, Target amounts, Progress records
Subscriptions
Service names, Providers, Costs, Billing cycles
Investments
Asset names, Initial/Current values, Performance notes
Contacts
Full names, Emails, Phones, Addresses, Company, Birthdays
Personal Notes
All titles and text content
Private Keys
Your RSA and ECDH private keys are also encrypted
Note: Every single field listed above is transformed into unreadable ciphertext before it leaves your device.
"We don't just lock your data; we build a fortress around it, where the only key that works is the one in your memory."