Group Data Sharing
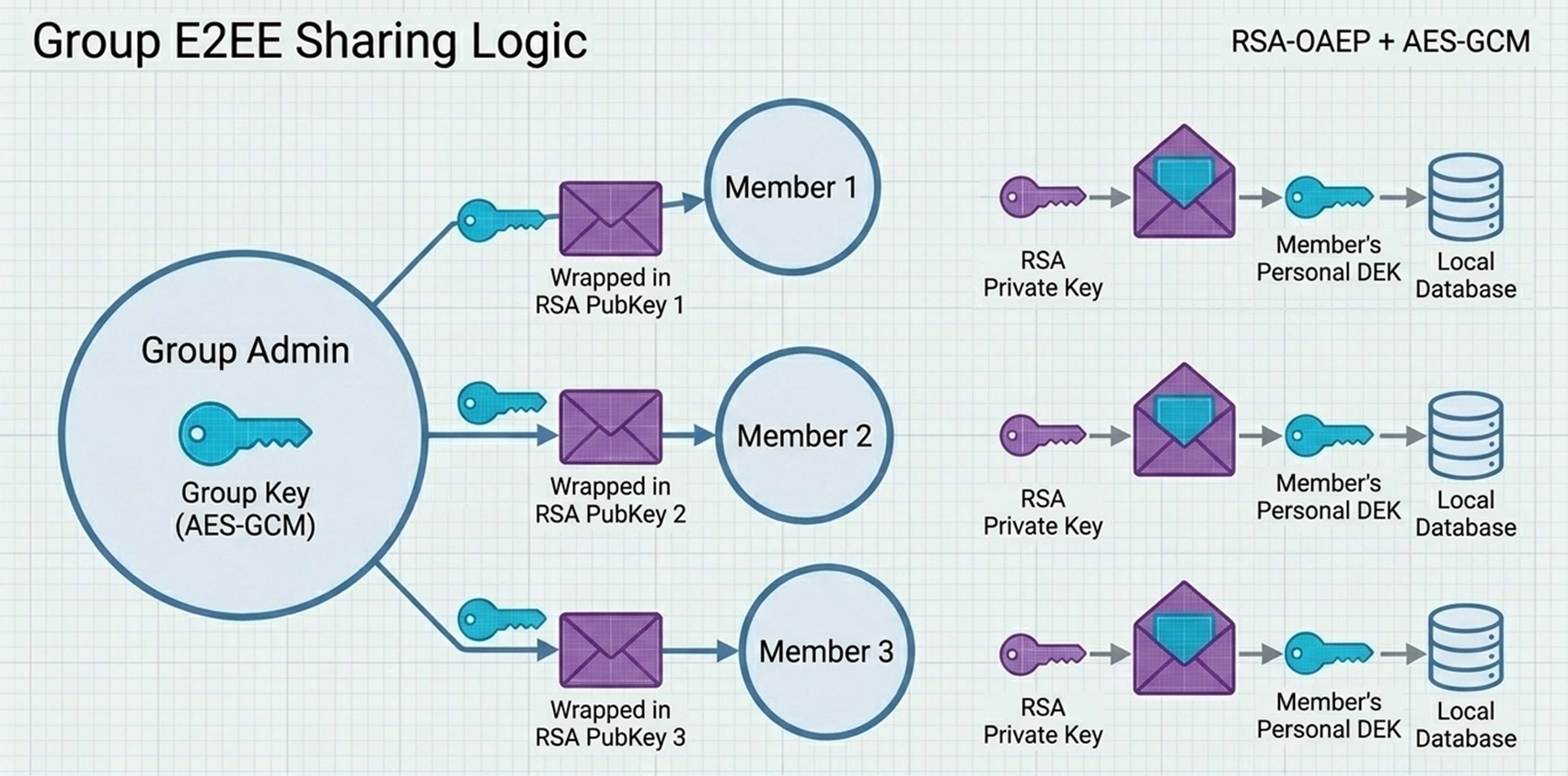
Collaborative finance with privacy. How we let multiple people access shared financial data without anyone sharing their master password.
The "Safe Deposit Box" Analogy
Imagine your family needs a shared locker in a bank. How do you give access to new members without copying keys?
1. The Shared Locker
When a group is created, we generate a unique Group Key (like a secret combination). This key opens all shared financial data for the entire group.
2. The Personal Safe
Each member has their own personal vault with two keys: a Public Key (anyone can use to lock something for you) and a Private Key (only you can use to unlock it).
How Members Get Access
When a new member joins, they receive the Group Key wrapped in a special secure envelope. They use their Private Key to open it, then store it safely in their personal vault for future use.
How It Works
A simple visual walkthrough of how the Group Key flows safely between members.
has access
new members
The Invitation Process
How a new member safely receives access to the group.
Owner Sends Invitation
- Owner retrieves the Group Key from their secure storage
- Owner's device looks up the new member's Public Key
- Group Key is wrapped securely for that specific member
- Invitation is sent to the group
Only the invited member's Private Key can unwrap this.
Member Joins Group
- Member receives the invitation
- They use their Private Key to unlock the Group Key
- They store it in their personal secure vault
- Now they can access group data!
The Group Key is now safely stored in their vault, protected by their master password.
What Happens If Someone Leaves?
Access removal happens at the database level, ensuring complete isolation.
Protection at Database Level
Former Member Has
Why Key Rotation Isn't Needed
Instead of complex key rotation, our system uses database-level protection. When someone leaves or is removed:
- •Their access entry is removed from the group's records
- •Our database security rules immediately block them—they can't query any group data
- •Even if they still have the Group Key locally, it becomes useless without database access
"In a Secure Group, your family's finances stay within the family—protected by two layers: strong encryption and database access rules."