1-on-1 E2E Messaging
Private conversations powered by End-to-End Encryption (E2EE). Even we cannot read your messages—only you and your partner hold the keys.
The Story of Alice & Bob
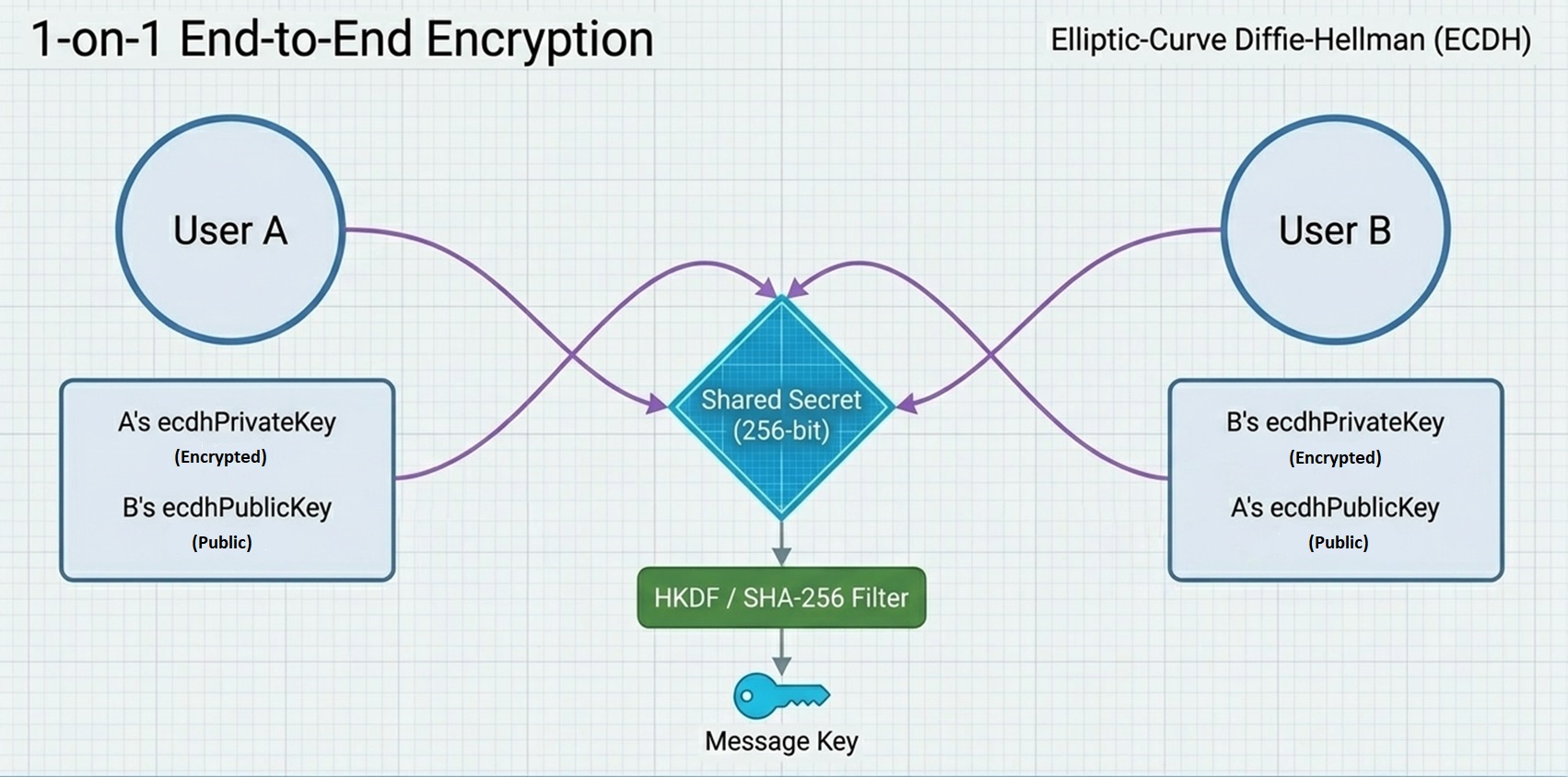
How two people create a secret mathematical language using cross-paired keys.
Shared Secret Key
The exact same 256-bit number is generated on both ends. This key is born on your devices simultaneously.
The Cross-Pair Magic
ECDH (Elliptic-Curve Diffie-Hellman) allows Alice and Bob to arrive at the same secret by swapping their Public Keys and mixing them with their own Private Keys.
Because of the mathematical properties of Elliptic Curves, both calculations yield the identical result.
An eavesdropper only sees the Public Keys passing through the network. Without the Private Keys, the Shared Secret is mathematically impossible to compute, even with the world's most powerful supercomputers.
Why is this so secure?
In traditional apps, the server holds the key. In SimpleMoneyTracker, the key is created on-the-fly by mathematics on your own device.
No Key Transit
We never send your Private Keys over the internet. They stay locked in your Personal Data Vault.
Zero-Server Access
Since our servers don't have your Private Keys, they can never calculate the Shared Secret. To us, your chat is just random noise.
Perfect Isolation
A shared secret between Alice & Bob is mathematically unique. It cannot be used to read messages between Alice & Charlie.
"Your conversations are a private whisper in a crowded room, where only you and your partner have the magic hearing aid to listen."